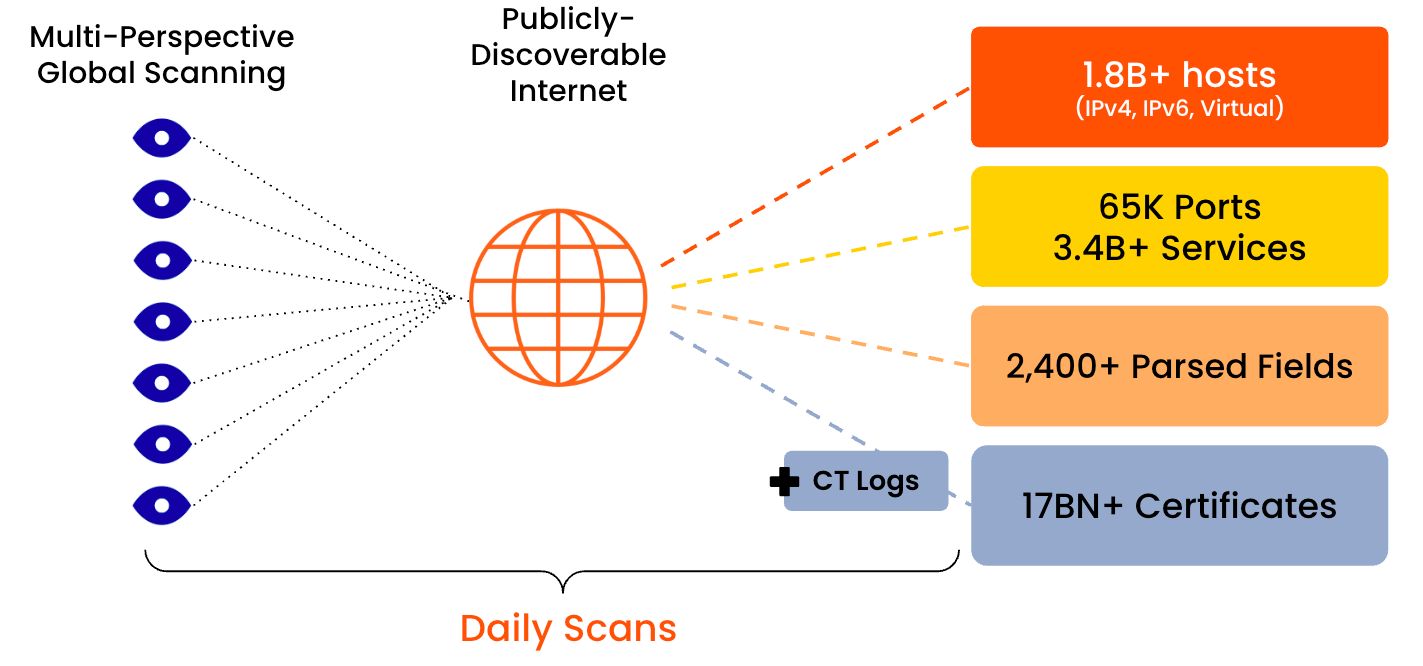
Censys discovers the devices, networks, and infrastructure on the Internet, and monitors, how it changes over time.
Censys partners with both the private and public sectors to provide the most accurate internet intelligence data available, so threat analysis teams can uncover risks and take down threats at scale.
Started in 2017 at the University of Michigan, Censys helps you protect your organization by discovering unknown assets and associated risks through its Censys Attack Surface Management Platform. Censys mines its market-leading Internet datasets and comprehensive certificate database as well as integrates with common cloud providers to uncover the hidden links between assets, surface unknown assets and risks, and provide a comprehensive Internet inventory.
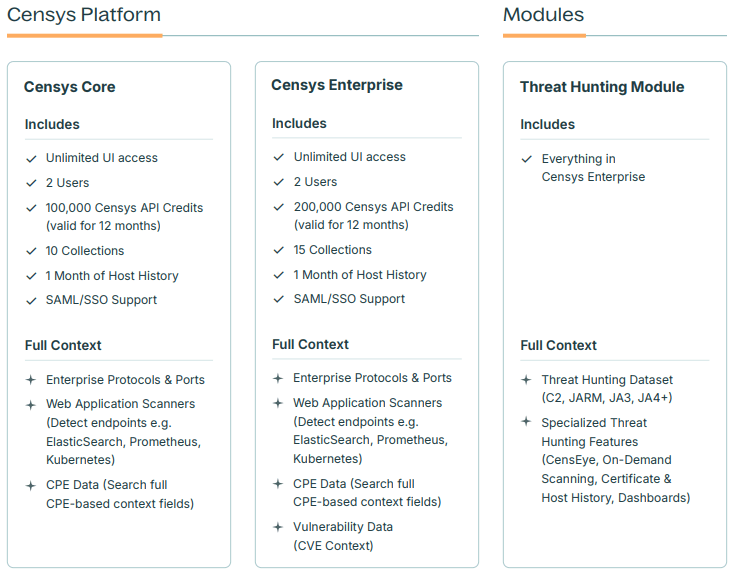
Censys Platform
The Platform is available in two core tiers: Censys Core and Censys Enterprise, and can be extended with powerful add-ons to meet the needs of any organization, from lean security teams to global enterprises and government agencies.
The Threat Hunting module, built for advanced adversary tracking and enriched analysis, is available exclusively with Censys Enterprise and cannot be purchased stand-alone.
Censys Attack Surface Management (ASM)
While the Censys Search Platform provides internet-wide visibility, Censys ASM utilizes that same data to focus exclusively on an organization’s own digital footprint. It provides a dedicated dashboard for discovering, inventorying, and monitoring all internet-facing assets from an external, “attacker’s perspective.”
- Continuous Asset Discovery: Automates the identification of external assets, providing an up-to-date inventory of the organization’s internet exposure.
- Cloud Exposure Management: Native integrations with the three major cloud providers allow for the identification of “Shadow Cloud” assets—resources residing outside sanctioned cloud accounts.
- Risk Prioritization: A configurable risk engine assigns severity ratings to exposures based on impact, exploitability, and likelihood, allowing teams to focus on the most critical vulnerabilities.
Key Technical Features:
- Discovery Path: Provides a detailed audit trail explaining why an asset was attributed to the organization, showing the connections and “pivots” made during discovery.
- Workspaces: Enables the logical separation of different environments, subsidiaries, or acquisition targets within a single platform.
- APIs and Integrations: Data can be natively exported to SIEM, SOAR, ticketing systems, and vulnerability scanners.
What sets Censys apart in the market is its ASM refresh frequency (up to hourly) and the Discovery Path feature. This functionality answers the most common question security teams face: ‘Is this really our server, or just a false positive?”
